
Backup Validation
ARE YOUR BACKUPS CLEAN AND RECOVERABLE?
Many organizations only discover corrupted or malware-infected backups during a crisis, when it’s too late. Gain true recovery assurance with Backup Validation, featuring AI-powered threat scanning, automated testing, and recoverability scoring.
-
Service
OverviewManaged Threat Detection for your Veeam Backups

Most backup tools simply confirm that your data was “saved”. What they can’t confirm is whether that data is clean. Dormant ransomware can silently infiltrate your backups before an actual attack, leaving no clean recovery point when you need it most. This blind spot is the Cyber Recovery Gap, and closing it is critical to how well you can bounce back after a cyber event.
We can help.
Recovery Point’s Backup Validation service reports on your backup health, elevating your understanding of your backup recoverability. By continually validating copies of your backups through automated testing in an isolated environment, we help identify your backups as recoverable, malware-free, and operational, thereby closing the Cyber Recovery Gap.
By adding Recovery Point’s managed Backup Validation threat detection, you’re not just backing up your data; you’re TESTING that backup frequently to ensure that it’s malware-free and ready to recover when you need it.
Benefits
-
Audit-Ready Proof
Simplify compliance, cyber insurance, and executive reporting with structured, automated validation reports. RECOVERABILITY SCORING provides proof of resilience you can share with auditors, insurers, and executives.
-
Intelligent Threat Detection
Ensure you have a clean recovery point by identifying possible dormant or embedded malware, bypassed by traditional XDR/EDR tools, using AI-POWERED advanced threat scanning.
-
Proactive Cyber Resilience
Be prepared by closing the Cyber Recovery Gap with continual validation through AUTOMATED TESTING. Proactive resilience turns backups into a reliable core layer of your cybersecurity defense strategy.
Cyber Recovery Readiness Assessment
Are your backups actually recoverable? Self-assess whether your backup and recovery strategy can withstand a real-world ransomware attack with our quick survey.
Stats
Backups are no longer a guaranteed safety net. Attackers now target backup systems directly, and too many organizations discover too late that their data can’t be recovered. These stats highlight why validated, provable recoverability is essential to cyber resilience.
-
93 %
of ransomware attacks now target backup infrastructure itself, making secure storage alone insufficient.
-
75 %
of companies faced failed backup recoveries after a cyberattack.
-
41 %
of companies that paid a ransom still failed to recover all their data.
-
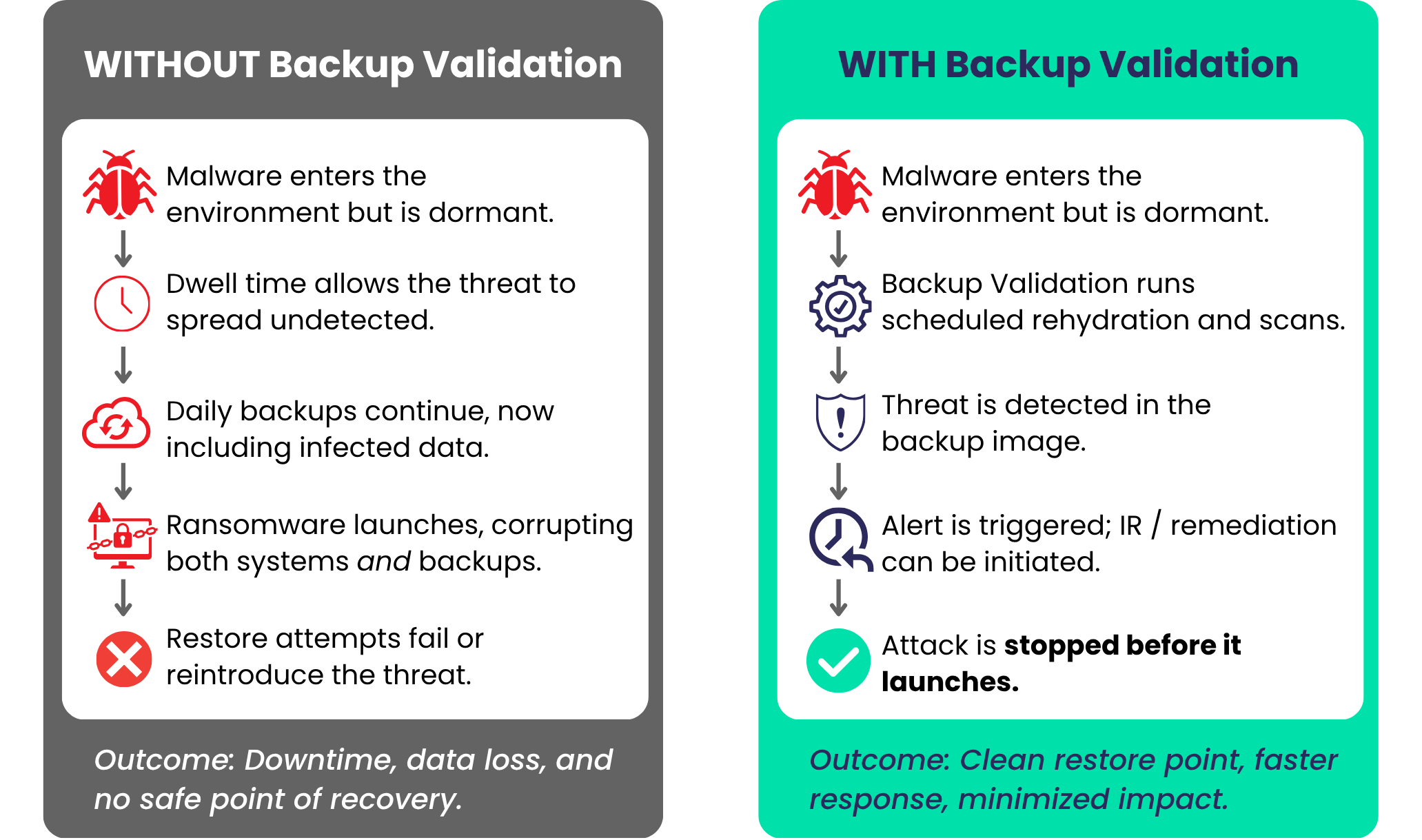 The Cyber Recovery Gap in Action
The Cyber Recovery Gap in ActionAnatomy of an Attack
Ransomware often spreads quietly, slipping into backups long before it detonates. What look like safe recovery points are already compromised, leaving restores to fail or reintroduce malware when it matters most.
Backup Validation changes that outcome. Backups are rehydrated and scanned in a secure cleanroom to catch threats early, trigger remediation, and provide a trusted path to fast, clean recovery.
How Backup Validation Works
1. Rehydrate backups in a safe, isolated cleanroom
Backups are automatically restored on schedule into a secure cleanroom to simulate real recovery.
2. Power on and test systems for real-world recoverability
Systems are booted and verified to ensure they start and function as expected – beyond just data integrity checks.
3. Scan for hidden malware and anomalies
Integrated malware and anomaly scans identify threats missed by production XDR/EDR tools.
4. Score and report on your recovery readiness
Quantifiable insights show the health and recoverability of your backups, delivering structured outputs for audit, regulatory, and cyber insurance needs.

Schedule a Free Consultation
Reach out today to start a conversation on how to harness predictive and proactive strategies to ensure you stay ahead of the next generation of disruptions.
Backup Validation - Contact Form
"*" indicates required fields



